How one click of the mouse cost a Melbourne business over $80,000

Last week I received some news that I never wanted to hear, one of our customers was targeted for an email scam which cost them big time and we were being tasked with working out the who/what/where/why.
The scam went something like this – our customer was involved in a legitimate transaction whereby they were going to pay a third-party a little over $80k. Everybody involved knew this transaction was about to take place, it was expected, in fact it was routine so it came as no surprise to our customer when they received an email detailing the specifics, including the bank account details of where the money was to be transferred.
The customer become concerned when they started receiving reports that the money they had paid had not been received, our client checked and double checked the bank account details and assured the other party that the money had been transferred, the funds had left their account the day before and the account number that was paid in to matched what they had been told, surely the money would turn up soon enough they thought.
What they didn’t know at the time was that someone had intercepted the original email, the one that detailed the bank account details, and had substituted the legitimate account numbers with their own. The trap had been set weeks before the transfer ever took place.
When it came time for the money transfer our customer quite happily paid it directly in to the scammers bank account without having any awareness at all that they had been scammed.
So how was it possible for the scammer to change the contents of the email? That was the next question we had to find the answer for.
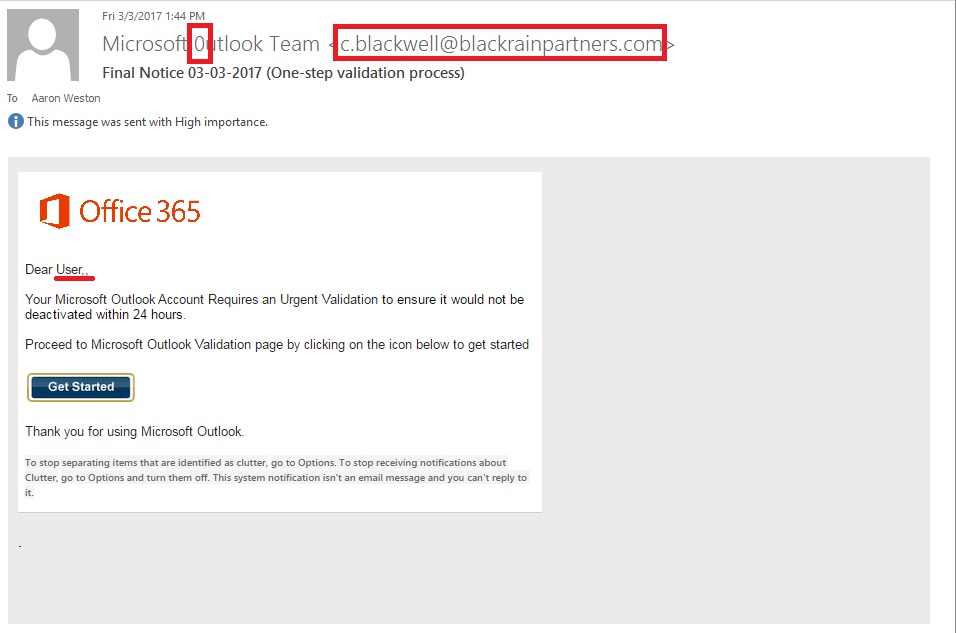
A common phishing scam cost this customer over $80,000
After a bit of digging around it became obvious what had happened, the person at our customers office who received the initial email (the one with the bank account details) had fallen victim to a phishing scam some time prior, potentially months earlier. We haven’t been able to find traces of the initial scam but it would have looked just like all the others out there, our customer received an email purporting to be from their ’email administrator’ telling them that their account was due to expire or that they were required to update their details or some other such thing and then directed our customer to a fake website whereby she typed her email address and password.
Now that the bad guys had her email password all they had to do was watch and wait for an opportunity to arise, they might have been watching for months or only a few days, we will probably never know.
Normally when telling such a story I like to finish by telling you that the good people of the world came together, found the scammer and recovered the money but I can’t tell you that because it didn’t happen. The money was transferred to a Suncorp bank account in Queensland and promptly disappeared. With a bit of luck, the Police investigation will eventually catch up with the criminals and our client might even get some of their money back, but I wouldn’t bet on it.
So, what’s the moral of the story?
Cyber security starts with the computer operator, all the security systems, antivirus software and firewalls in the world could not have prevented this attack. There are only two ways I can think of that could have prevented this- more vigilance on the part of the computer operator so as not to be duped by a common phishing scam and better business procedures to ensure that the bank account details were verified before the transfer.
The customer that was scammed is not a big business, losing over $80,000 is going to have a huge impact on them and is sure to result in many sleepless nights. I hope that the law will eventually catch up with the bad guys and that our customer can somehow recover from this.
Before publishing this we sought our customer’s permission to tell their story, they hope, as do I that by telling you what happened you can prevent it from happening to you too.
Our Services

Managed IT Support
Our fixed price Managed IT Support Programs will increase your businesses competitiveness and efficiency with our I.T. Professionals on call for you 24/7.

Same Day On-Site Support
Class leading response times ensure your that when things do go wrong we’ll be there in a hurry so you can get on with doing what your business does best.

Security and Data Protection
Custom designed security and data backup systems protect your business from emerging threats and gives you peace of mind.

Hardware and Software
We supply, install and maintain hardware and software from all major vendors including Hewlett-Packard, Microsoft, IBM, Intel and Dell all with our 30 day reconfiguration guarantee.
Testimonials

Thanks for all your help today. Your patience & tenacity for solving the problem is greatly appreciated.
Jacinta

They’ve gotten to know our business so well and they’re truly interested in helping us. It’s like having our own I.T. Department in-house. Australia Wide I.T. takes a personal interest in our team, our business and where we’re going. They’re like family.
Other I.T. companies just didn’t seem to have the same depth of knowledge as these guys. Rather than blame the user (us) they go the extra mile, locate the problem and fix it – Every time!
Coral

A very big thank you from me to all of the guys there….You make things so easy for us and are always available to help.
A massive shout out to the Nash though for fixing our printer – you nailed it Nash and not only changed MY life, but also helped to save some trees in the Amazon Forest!
Thanks to you all.
Jo

Attentive and thorough, Australia Wide I.T. get onto any of our I.T. problems quickly – with prompt, friendly and efficient service. Whenever we need to upgrade, we know we can trust their knowledge in supplying flawless new equipment that always works both physically, and to suit our needs.
Alison

All good as usual, keep up the professional service.
Diana

Very much appreciate your very quick response today. It was pay day today and I was a bit worried (that we wouldn’t be able to process the pays) but because of you all is well, so a big thanks.
Dale

My business has grown from 3 stores to 5 stores over the last 3 years; one of the unfortunate consequences of this has been the fact that our old server and network could not cope with the growth. After much deliberation we chose Australia Wide I.T. to not only arrange the supply and installation of our new network, but to also provide long term support. We have been very pleased with our decision and would happily recommend them.
Bruce

Our previous I.T. Service Provider was distant, hard to contact and not customer focused. With Australia Wide I.T. we now have great service with a human touch. Our calls are answered promptly and the team is always ready to help in any way.
The maintenance program put in place by AWIT offers us peace of mind that our entire system is correctly and closely monitored.
Monica

The team at AWIT deliver nothing but breathtaking service!!!!
Brett

Your work last week was amazing. You couldn’t have been more supportive or expert in your conduct. I am very grateful and am amazed at your generous invoicing of last week’s work. I can only repay you by recommending you to as many people as possible.
Thank you. It is refreshing to know that when a problem occurs, you are always there – with great service.
Keran